Safety provided for all industries
For the company affected by a cyberattack, the damage can be immense. The consequences range from operational disruptions or failures to data loss and competitive disadvantages due to industrial espionage. Cyberattacks on critical infrastructure can also have a significant impact on the supply of essential goods or services (e.g., electricity, water, or medical care) to the public. To counteract the risk of cyberattacks, a systematic approach to IT/OT security is strongly recommended. For critical infrastructure as defined in the Regulation on the Determination of Critical Infrastructures of the Federal Office for Information Security (BSI-KritisV), the BSI act even sets legal obligations to implement minimum security standards.
Extensive experience in the industry, infrastructure and life science markets as well as expertise in sector-specific standards make infoteam a perfect partner for the implementation and operation of an information security management system (ISMS) that not only covers your company’s classic IT but also OT (operational technology). Our experts will reliably support you when it comes to fulfilling the Federal Office for Information Security’s recommendations (IT-Grundschutz) and the ISO/IEC 27001 standards.
Why OT security is so important
Annually, 3.3 million hours of production time are lost due to unplanned machine downtime. The German economy incurred €223 billion in damages in 2021 alone due to cyberattacks. Specific security measures and end-to-end security concepts can significantly reduce the risk of a successful cyberattack or substantially mitigate the consequences of one.
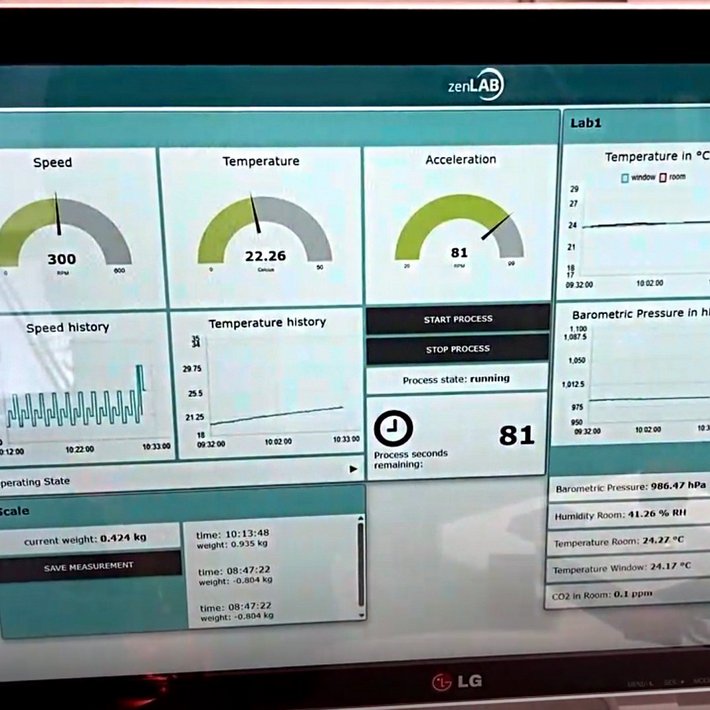
We support you with mapping IT/OT structures and analyzing them for weak points and potential hazards. We work with you to develop strategies for assessing and managing the cyber risks your organization is exposed to. infoteam boasts in-depth technology, software product and platform expertise and a wealth of experience from a wide range of industries. This enables our security experts to plan and implement security measures independently of manufacturers.

Secure software life cycle in the industry, infrastructure and digital health sectors
The security of products and processes heavily depends on the security of the software deployed, and this begins well before its intended use. Security must play a significant role throughout the entire software life cycle. In addition, the implementation of a secure software life cycle must be transparent and traceable, especially if the software is to be used in a highly standardized environment, such as in medical technology.
Under the maxim “Security right from the start,” infoteam offers tailor-made concepts and solutions for your data security. The concepts can be added into the areas concerned in a project- and customer-specific way or can supplement the development process, allowing you to take security aspects into account right from the start.
Training as a Secure Software Engineer also offers your employees the opportunity to gain or deepen the most important basic knowledge on the subject of secure software. The training program is offered by infoteam together with the IT expert network Arbeitskreis für Software-Qualität und Fortbildung (ASQF).
Why software security concepts pay off
- 3.3 million hours of production time are lost annually due to unplanned machine downtime
- 47% of ransomware attacks target operational technology and control systems
- €100,000 is the average cost of one hour of unplanned machine downtime
Only 21% of companies have mature OT security programs. As a result, 79% of companies are at risk of unplanned machine downtime and its expensive consequences.


This is how infoteam helps you to efficiently rethink your security strategy
- IT/OT security right from the start:
- Security throughout the entire product and plant life cycle, from development to decommissioning
- For new developments
- In modernization projects
- Information security management for systematic and efficient handling of IT and OT security risks in your organization:
- Establishment of asset and risk management
- Definition and implementation of measures
- Employee awareness
- Certification preparation and training
- Security throughout the entire product and plant life cycle, from development to decommissioning
- Cyber-resilience maximization